We’re massive fans of Cloudflare and deploy it as part of our speed optimization services.
Cloudflare has an amazing range of features and options and a lot of the features go unused or under leveraged. In this post we’ll share three Cloudflare that will both help improve the security or your WordPress site and at the same time also reduce the load on your site and help speed it up.
These are really easy to setup and if you’re moderately tech savvy will take you maybe 10-15 minutes. Click the images to enlarge.
These rules and settings with not only improve your site security but they’ll reduce load on your site, improve your site speed and may also help give your site an SEO boost.

Table of Contents
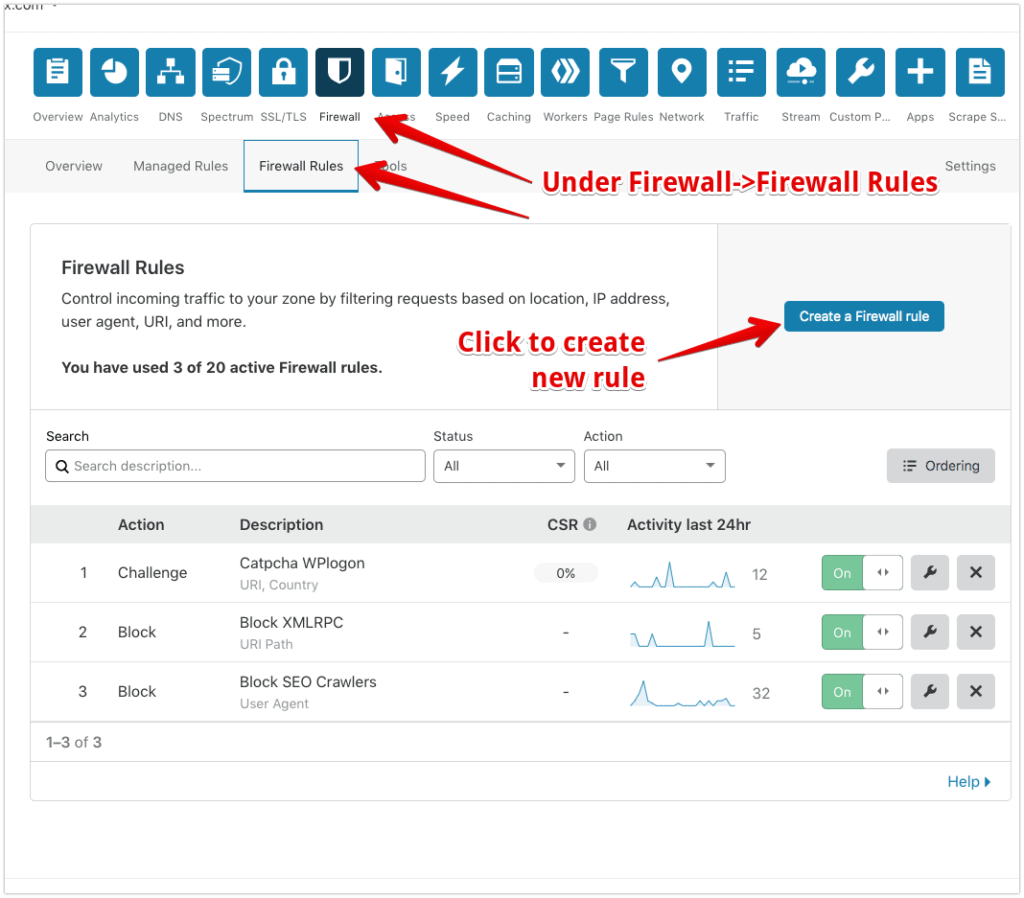
How to add Cloudflare Firewall rules
Firewall rules can be added under the Firewall menu->Firewall Rules tab in Cloudflare. The free plan gives you up to 5 rules so these can be added at no cost.
Once you add a rule it takes effect almost immediately.
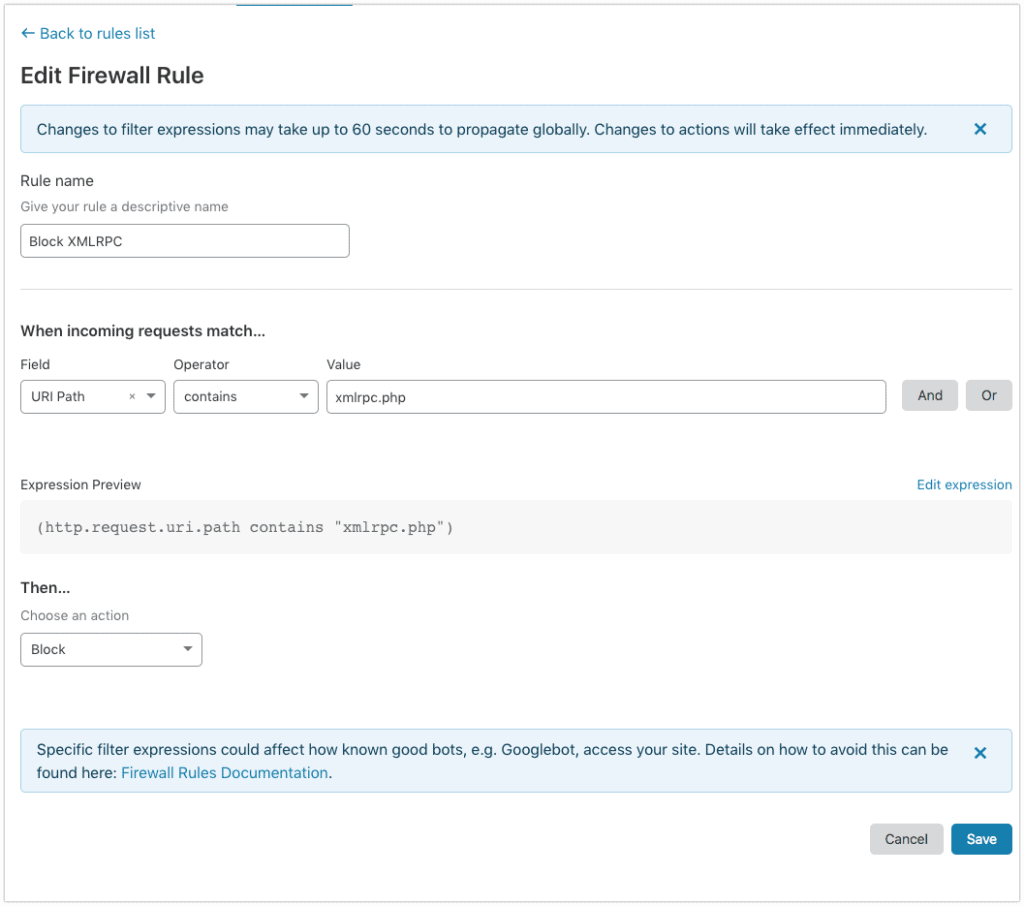
1. Block access to XMLRPC.php
This is an older WordPress API interface that is very rarely used but is a vector for many attacks.
Hammering this file with requests can very quickly chew up a lot of CPU cycles and on a shared host or host with low CPU or resources available it may start throwing 502 and 504 errors.
2. Block SEO Bots & Crawlers
With this rule we block traffic from Ahrefs, Semrush and Opensite explorer (SEO Moz bot) SEO bots.
These are extremely aggressive crawlers and particularly on Woocommerce they’ll rapidly add and remove things from the cart multiple times per second again chewing a lot of CPU resources.
In addition, allowing them to crawl the site will also divulge some SEO information that competitors using these SEO tools may find useful.

3. Block Brute Force Attacks On The WordPress Logon Page
The typical WordPress site we see can get anywhere from 1000-10000 brute force logon attempts a day.
Adding a rule to show a captcha message to visitors hitting this page OR visitors hitting this page outside the home country of the site can dramatically reduce brute force password attempts and reduce a lot of load on the hosting.
Copy and paste the code in the box below into the “edit expression” in the rule setup which will create this rule for you:
(http.request.uri contains "wp-login.php" and not ip.src.country in {"US"})
4. Filter Traffic Outside Your Target Country
This is a fantastic rule for sites in highly competitive industries where things like negative SEO or hacking attempts are common.
This rule will run traffic outside your target country through a Cloudflare Managed Challenge and will filter non-genuine traffic. We’ve used this rule or variations of it on 100s of sites to protect against all sorts of attacks including things like click fraud.
Note that the “well-known” rule is in place so as not to break the SSL certificate generation/renewal process and the “uptime” user agent rule will stop uptime tools from being blocked.
This rule WILL block legitimate third party apps and APIs if you’re using them so you’ll need to add additional user agents as needed for whatever tools you’re using with your site.
You can also filter by continent, for example for if your site is targeting the EU and you can filter traffic outside of Europe.
You can copy and paste the code below into the “edit expression” box and it’ll create this rule for you:
(not ip.src.country in {"US" "CA"} and not cf.client.bot and not http.request.uri.path contains "well-known" and not http.user_agent contains "uptime")
5. Enable HSTS For Better Security, Lower TTFB and *Maybe Better SEO
HSTS stands for HTTP Strict Transport Security – with HSTS enabled, your site will be more secure, will load faster for repeat visitors via improved TTFB timings and in some cases we’ve seen SEO ranking improvements as a result as in some cases it can resolve canonical SEO issues.
You can enable HSTS inside Cloudflare’s SSL settings to achieve this BUT note that you MUST have an SSL certificate before you enable HSTS otherwise your site may become inaccessible.
Membership sites and WooCommerce sites will benefit the most from enabling HSTS, as typically those are dealing with sensitive user data and typically have more repeat visitors, but all types of sites will benefit from enabling it.
The HSTS settings are available under SSL/TLS->Edge Certificates – click play on the video for a walkthrough

Related Posts & Resources
SiteSpeedBot Website Speed Test Tool